Cyber risk is no longer an IT discussion.
For branding agencies, it is a reputational, financial and contractual risk that sits squarely at board level.
AI-enabled attacks are increasing in speed, realism and scale. Agencies are being targeted not just for their own assets, but as gateways into client organisations.
This briefing outlines what directors need to understand — and what decisions sit at board level.
📌 The Current Threat Landscape (2026 Reality)
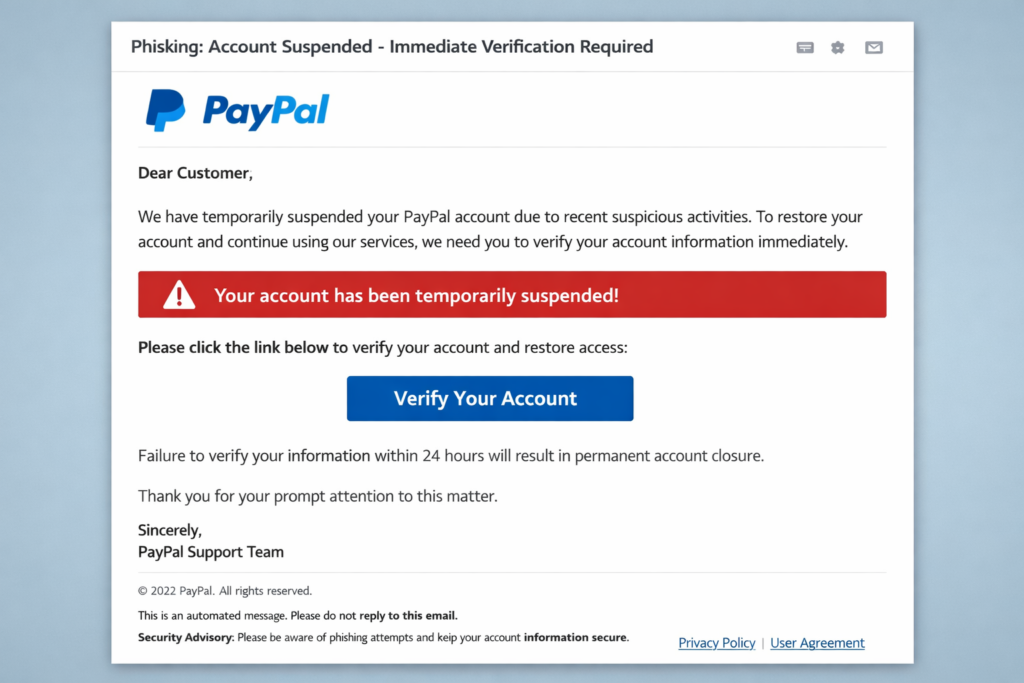
AI-Enhanced Phishing & Invoice Interception
- Highly personalised email fraud
- Payment diversion scams
- Thread hijacking in long-running client conversations
UK Finance continues to report significant authorised push payment fraud affecting UK businesses.
Supply Chain Targeting
Agencies are attractive because they hold:
- Pre-launch brand intelligence
- CMS access
- Social media control
- Domain registration rights
Attackers may view agencies as weaker security links in a client’s ecosystem.
The National Cyber Security Centre warns that AI lowers the barrier to entry for attackers and increases attack volume.
🔗 https://www.ncsc.gov.uk/collection/small-business-guide
💼 Board-Level Risk Categories
1. Financial Risk
- Invoice interception
- Ransomware downtime
- Regulatory fines
- Litigation costs
Single six-figure losses are not uncommon in UK invoice diversion cases.
2. Reputational Risk
- Public disclosure of breach
- Loss of enterprise clients
- Loss of pitch credibility
- Press coverage damage
For a branding agency, reputational damage may exceed direct financial cost.
3. Legal & Regulatory Exposure
Under UK GDPR, agencies processing client or user data must demonstrate appropriate security measures.
The Information Commissioner’s Office can investigate failures in data protection governance.
🔗 https://ico.org.uk/for-organisations/uk-gdpr-guidance-and-resources/artificial-intelligence/
4. Contractual Liability
Enterprise clients increasingly include:
- Security clauses
- Breach notification timelines
- Cyber assurance requirements
Failure to meet obligations may trigger contract termination.
🛡️ Governance Responsibilities at Director Level
Cyber security cannot be delegated entirely to IT or operations.
Directors should ensure:
Clear Accountability
- Named board-level cyber lead
- Defined incident escalation route
- Annual board review of cyber posture
Financial Control Oversight
- Dual approval for payment changes
- Documented payment verification policy
- Quarterly audit of financial controls
Access & Identity Governance
- Mandatory MFA across agency
- Offboarding process for staff & freelancers
- Quarterly access review
🔐 Minimum Security Baseline for Agency Operations

Technical Controls
- Multi-factor authentication (MFA) everywhere
- Centralised password management
- Encrypted backups (offline or immutable)
- Regular patching discipline
Organisational Controls
- Phishing awareness training
- Defined incident response plan
- Supplier cyber requirements
- Annual tabletop cyber simulation
Certification Consideration
Cyber Essentials certification provides a baseline security framework recognised across UK supply chains.
🔗 https://www.ncsc.gov.uk/cyberessentials/overview
🎙️ Emerging Risk: AI Voice & Executive Impersonation
AI voice cloning tools are widely available.
Potential scenarios:
- “Managing Director” requests urgent payment
- “Client CEO” requests domain transfer
- Fake supplier deposit request
Board directive required:
No financial approvals via voice alone.
Dual written verification mandatory.
📊 Strategic Questions Directors Should Ask
- Do we have MFA enabled on every system?
- Could we restore from backup within 24–48 hours?
- Who speaks to clients in a breach scenario?
- Do we know our contractual breach notification deadlines?
- Have we tested our incident response plan in the last 12 months?
If the answer to any is “no” or “unsure”, that is a board-level gap.
📈 2026–2031 Outlook for Agency Directors
Expect:
- Increased targeting of agencies as supply chain entry points
- Clients demanding formal cyber assurance statements
- Insurers requiring stricter controls
- More regulatory scrutiny after publicised breaches
Agencies that can demonstrate cyber maturity will gain competitive advantage in enterprise tenders.
🧾 Board-Level Action Plan (Next 90 Days)
Month 1
- Confirm MFA across all systems
- Review financial control processes
- Assign board cyber lead
Month 2
- Conduct external vulnerability assessment
- Review supplier access
- Confirm backup testing
Month 3
- Conduct tabletop cyber simulation
- Review incident response communications
- Assess Cyber Essentials readiness
🧠 Final Message to Agency Directors
Cyber risk is brand risk.
For a branding agency, trust is currency.
A breach damages more than systems — it undermines credibility.
The majority of AI-enabled attacks still succeed due to:
- Weak payment controls
- Missing MFA
- Poor access management
- Untested backups
Those are governance issues — not technical mysteries.
Directors who treat cyber resilience as a strategic asset will protect revenue, reputation and long-term client trust.
Accelerate Your Learning
We have created Professional High Quality Downloadable PDF’s at great prices for UK Businesses provided to you from our main website. Which include various helpful Cyber related documents and real world scenarios your business might experience, showing what to do and how to protect your business. Find them here.