The uncomfortable truth for UK SMEs
Small and medium businesses across the UK remain the cybercriminal’s favourite snack. Not because they’re unlucky. Because they’re easier to break into than a garden shed with a polite knock.
According to the National Cyber Security Centre, the majority of successful attacks still exploit basic weaknesses: poor passwords, unpatched systems, and human error.
“Cyber security is not just an IT issue, it is a business risk.” — NCSC guidance
The Biggest UK Cyber Stories This Week
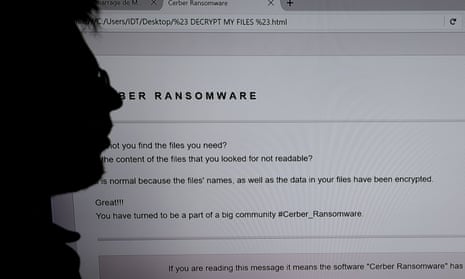
Ransomware Attacks Continue to Target UK SMEs
Why SMEs are still easy targets
Ransomware groups are not getting smarter. They’re just getting more efficient at exploiting the same predictable mistakes.
Recent reporting from Action Fraud highlights:
- Increased ransomware incidents targeting firms with under 50 employees
- Attacks often start with a phishing email or compromised login
- Backup systems frequently either don’t exist or fail when needed
The criminals don’t need sophistication. They need consistency. SMEs supply that in abundance.
Expert insight
The National Crime Agency has repeatedly warned:
“Ransomware remains the most significant cyber crime threat to UK organisations.”
Charming. Reassuring. And still somehow ignored.
Business Email Compromise (BEC) Is Quietly Costing Millions
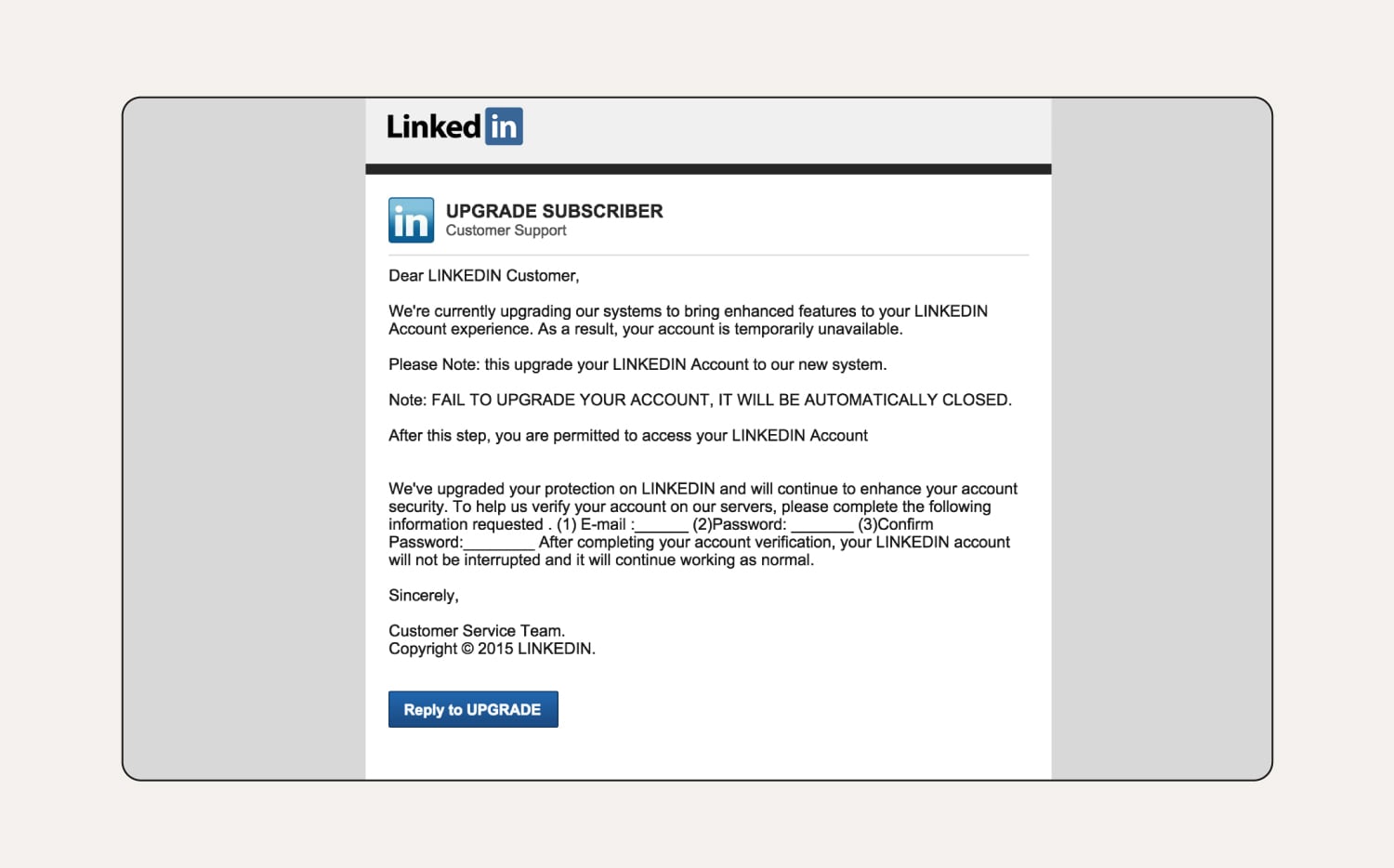
Forget Hollywood-style hacking. The real damage comes from emails that look boring and legitimate.
BEC scams involve:
- Fake invoices that look identical to real suppliers
- Spoofed email addresses mimicking directors or finance staff
- Payment diversion requests at “urgent” moments
According to UK Finance:
Authorised push payment (APP) fraud losses remain in the hundreds of millions annually.
That’s not a typo. That’s your industry quietly bleeding cash.
Why SMEs fall for it
- No dual approval processes
- Staff afraid to question “senior” emails
- Weak email authentication (SPF, DKIM, DMARC barely understood, let alone configured)
AI-Powered Cybercrime Is No Longer Theoretical
The problem just evolved
Tools once discussed like sci-fi nonsense are now actively used by criminals:
- AI-generated phishing emails with near-perfect grammar
- Deepfake voice scams impersonating CEOs
- Automated vulnerability scanning targeting small businesses
The Europol has warned:
“AI is lowering the barrier to entry for cybercrime.”
Translation: you no longer need to be clever to be dangerous.
UK SME impact
- More convincing scams
- Faster attack cycles
- Higher success rates against untrained staff
So yes, the threat landscape just got worse. Not dramatically. Just enough to hurt.
Supply Chain Attacks Creeping Into Smaller UK Firms
You’re only as secure as your worst supplier
Many SMEs assume they’re too small to be targeted directly.
They’re right. They’re targeted indirectly instead.
Recent UK-focused advisories from the National Cyber Security Centre highlight:
- Compromised SaaS platforms used by SMEs
- Weak vendor credentials exploited to access multiple businesses
- Shared systems becoming entry points
The uncomfortable reality
You can do everything “right” internally and still get breached because:
- Your accountant uses weak passwords
- Your IT provider hasn’t patched systems
- Your cloud vendor gets compromised
Security is now a group project. And someone in the group always does nothing.
Advertisement
- STAY CONNECTED ON YOUR TERMS: Be seen and heard clearly and securely with a HP True Vision camera and background noise-r…
- YOUR ALL-DAY, ANYWHERE PRODUCTIVITY POWERHOUSE: Face the day with an AMD Processor , long battery life, ample storage, a…
- AMD RYZEN 5 PROCESSOR: Tap into truly impressive notebook performance. A revolutionary new architecture with amazing bat…
- 【Processor】 AMD Ryzen 5 7530U (6 Cores, 12 Threads, 16MB L3 Cache, 3MB L2 Cache, Base Frequency at 2.0GHz, Up to 4.5GHz …
- 【Display】 15.6 inch Non-Touch Display, FHD (1920 x 1080), IPS, narrow bezel, anti-glare, 250 nits, 45% NTSC.
- 【RAM and Storage】 Up to 64GB DDR4 RAM. Up to 4TB PCIe M.2 SSD.
Key Cyber Trends UK SMEs Cannot Ignore
Human Error Still Wins
The weakest link refuses to evolve
The Department for Science, Innovation and Technology Cyber Security Breaches Survey consistently shows:
- Staff errors remain a leading cause of breaches
- Phishing success rates remain stubbornly high
- Training is either absent or ineffective
Technology improves. Humans click things.
Cyber Insurance Is Getting Harder (and Pricier)
Insurers are finally paying attention
UK insurers are tightening requirements:
- Mandatory MFA (multi-factor authentication)
- Evidence of patch management
- Incident response plans
Translation: you can no longer buy your way out of negligence.
Regulators Are Paying More Attention
Compliance is no longer optional theatre
With frameworks like:
- Information Commissioner’s Office
- UK GDPR enforcement
Fines and reputational damage are becoming more common for:
- Data breaches
- Poor data handling
- Failure to report incidents
Ignoring cyber security is now both risky and expensive. Impressive combination.
What UK SMEs Should Actually Do (Not Just Talk About)
The basics that still aren’t done
Start here before buying anything expensive
- Enforce multi-factor authentication across all systems
- Use password managers instead of “Summer2024!” everywhere
- Regular offline backups tested monthly
- Apply software updates promptly
Revolutionary, apparently.
Staff Training That Isn’t Useless
Annual slide decks don’t count
- Run simulated phishing tests
- Train finance teams specifically on invoice fraud
- Encourage questioning unusual requests
Fear-based silence is exactly what attackers rely on.
Email Security Controls
The unglamorous fix that stops real attacks
- Configure SPF, DKIM, DMARC properly
- Monitor domain spoofing
- Use secure email gateways
It’s not exciting. It works.
Incident Response Planning
Because “panic” is not a strategy
- Define roles before an incident
- Know who to call (legal, IT, comms)
- Practise response scenarios
If your plan is “figure it out when it happens,” congratulations, you already lost.
Final Reality Check for UK SMEs
Cybercrime in the UK isn’t slowing down. It’s industrialising.
Attackers:
- Automate
- Scale
- Reuse proven tactics
SMEs:
- Delay
- Assume
- Hope
That mismatch explains most breaches.
The gap isn’t technology. It’s discipline.
References and Further Reading
- National Cyber Security Centre
https://www.ncsc.gov.uk - Action Fraud
https://www.actionfraud.police.uk - National Crime Agency
https://www.nationalcrimeagency.gov.uk - UK Finance
https://www.ukfinance.org.uk - Information Commissioner’s Office
https://ico.org.uk - Europol
https://www.europol.europa.eu
If nothing else, here’s the blunt takeaway: most UK SMEs aren’t being outsmarted. They’re being out-prepared. And somehow, week after week, that continues to surprise people.
Accelerate Your Learning
We have created Professional High Quality Downloadable PDF’s at great prices for UK Businesses provided to you from our main website. Which include various helpful Cyber related documents and real world scenarios your business might experience, showing what to do and how to protect your business. Find them here.