UK organisations are being targeted constantly, mostly because attackers are lazy and scale beats brilliance. The latest UK Government Cyber Security Breaches Survey found phishing is still the dominant cyber crime reported by organisations experiencing cyber crime, and ransomware prevalence has risen year-on-year.
Below are the top 5 cyber security concerns UK businesses should care about this week, and likely next week too, because humans do love repeating mistakes.
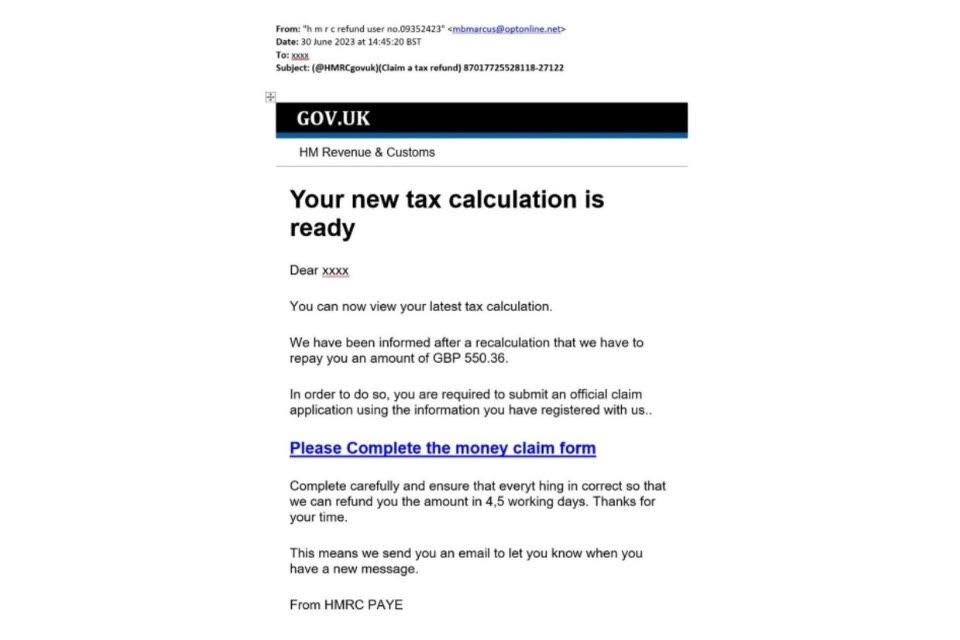
1) Phishing and BEC: the “tax rebate” lie that keeps paying
Phishing remains the most prevalent cyber crime type in the UK survey results, and it’s the launchpad for everything else (credential theft, payment diversion, malware).
What it looks like in real UK businesses
- Fake supplier invoices (“bank details changed, please pay urgently”)
- “New payroll file attached” emails to HR
- Executive impersonation (classic BEC) timed around month-end or payday
- Brand impersonation (HMRC, couriers, Microsoft 365 logins) to harvest passwords
Why it’s still winning
Because it targets your people and processes, not just your tech. It also scales: one decent lure can hit thousands of inboxes before lunch.
What to do now (practical, not magical thinking)
- Enforce MFA everywhere, especially email and finance tooling
- Add payment-change controls: call-back using known numbers, dual approval
- Turn on strong email authentication (DMARC/DKIM/SPF) and monitor failures
- Run short, frequent phishing drills focused on invoicing and payroll scenarios

2) Ransomware and extortion: downtime is the real ransom note
The Breaches Survey estimates the share of businesses experiencing a ransomware crime increased (from under 0.5% to 1%), equating to around 19,000 businesses.
Government has also been pushing international guidance aimed at stopping ransomware attacks that disrupt supply chains and critical services.
What it looks like
- Encryption + “pay or we leak your data”
- Attacks that start with stolen credentials (often from phishing) and then move fast
- Insurers and incident responders getting called after the attacker already has domain admin (classic)
Expert view
CrowdStrike’s CEO put it bluntly: “AI systems themselves become part of the attack surface.”
What to do now
- Keep offline / immutable backups and test restores (actually test them)
- Segment networks (finance, ops, backups should not be a flat shared playground)
- Remove local admin rights by default; harden remote access
- Have an incident plan that includes who decides on shutdowns, comms, legal, insurers
3) Supply chain and third-party compromise: your partners are your perimeter now
Attackers increasingly go after suppliers because it’s cheaper than attacking you directly. UK guidance and policy messaging is heavily focused on spotting weaknesses in supply chains before criminals do.
What it looks like
- MSP compromise leading to multiple customers getting hit
- Stolen vendor credentials used to access your systems
- Compromised software updates or tools in the build pipeline (CI/CD)
Why UK firms are exposed
UK business is full of outsourced IT, cloud services, agencies, contractors, and “temporary” integrations that become permanent.
What to do now
- Rank suppliers by risk (who can access what, and what happens if they’re breached)
- Require MFA, logging, and breach notification clauses for critical suppliers
- Rotate and minimise shared credentials; prefer scoped access + just-in-time privileges
- Monitor supplier access like it’s your own privileged users (because it is)
4) Unpatched vulnerabilities and internet-facing systems: the “we’ll do it next sprint” breach
When an edge system gets a critical vulnerability, attackers automate exploitation fast. Recent waves have included high-impact SharePoint vulnerabilities, with Microsoft issuing urgent customer guidance to patch quickly.
UK-focused alerts also consistently urge “patch by default” and fast patching of exposed devices when critical issues emerge.
Advertisement
- PRE-PAID SUBSCRIPTION WITH SIGN UP AND ACTIVATION ONLINE: A payment method (credit card or PayPal) must be saved in your…
- SUBSCRIPTION WITH AUTOMATIC RENEWAL: No service disruption since this subscription automatically renews annually. If you…
- Protect multiple devices, including PCs, Mac, smartphones and tablets, against malware, phishing and ransomware with add…
What it looks like
- Old VPNs, firewalls, file transfer tools, SharePoint, Exchange, or remote management consoles exposed to the internet
- Patch windows delayed because “business can’t handle downtime”
- One compromised server becoming a launchpad across the estate
What to do now
- Maintain a living inventory of all internet-facing assets (if you can’t list it, you can’t secure it)
- Patch critical edge vulnerabilities fast, or isolate/remove from internet until patched
- Turn on attack-surface reduction: WAF, IP allowlists, admin portals behind VPN, EDR coverage
5) AI-accelerated attacks and identity abuse: faster intrusions, dirt-cheap persuasion
AI isn’t “the hacker”; it’s the multiplier. The trend is speed: shorter time from access to impact, better phishing copy, more convincing fake personas, and more attacks on AI-enabled workflows themselves.
What it looks like
- Hyper-personalised phishing (pulled from LinkedIn, Companies House filings, press releases)
- Prompt-injection attempts targeting AI email triage or internal copilots
- Credential theft leading to SaaS takeover and data exfiltration rather than noisy malware
Expert view
CrowdStrike’s Adam Meyers warned: “AI is compressing the time between intent and execution.”
What to do now
- Treat identity as the control plane: conditional access, MFA, device compliance
- Lock down OAuth apps and third-party integrations (least privilege, approvals)
- Log and alert on impossible travel, token abuse, mass downloads, unusual mailbox rules
- If you’re deploying AI tools internally: define what they can access, and monitor inputs/outputs
The major threats UK businesses face (in plain English)

Cyber crime (profit-driven)
Phishing, BEC, ransomware, extortion, and data theft at scale. The Breaches Survey shows huge volume and repeat targeting among victims.
Disruption risk (services and operations)
Recent warnings highlight disruptive attacks aimed at essential services and organisations not keeping up with resilience basics.
State-backed activity (strategic)
The NCSC Annual Review notes state actors remain a significant threat and that nationally significant incidents hit record levels.
“What this means for you” (the uncomfortable but useful bit)
If you’re an SME
Attackers aren’t picking on you personally. They’re scanning for weak MFA, exposed services, and sloppy payment processes, then moving on. The UK survey data suggests volume is the point.
If you’re mid-market or enterprise
Your risk is blast radius: supplier access, identity sprawl, and complex estates where patching and visibility are never quite finished.
If you run critical operations
Your board-level risk is downtime and trust. The UK’s resilience messaging is increasingly blunt: disruptive attacks are plausible and planning matters.
Sources and further reading (all live links)
- Cyber Security Breaches Survey 2025 (UK Government): https://www.gov.uk/government/statistics/cyber-security-breaches-survey-2025/cyber-security-breaches-survey-2025
- NCSC Annual Review 2025 (PDF): https://www.ncsc.gov.uk/files/ncsc-annual-review-2025.pdf
- UK Government: ransomware and supply-chain guidance launch: https://www.gov.uk/government/news/uk-leads-global-fight-to-stop-ransomware-attacks-on-supply-chains
- HMRC examples of phishing/scam messages (useful for staff training): https://www.gov.uk/government/publications/phishing-and-bogus-emails-hm-revenue-and-customs-examples/phishing-emails-and-bogus-contact-hm-revenue-and-customs-examples
- Microsoft guidance on SharePoint vulnerability CVE-2025-53770: https://www.microsoft.com/en-us/msrc/blog/2025/07/customer-guidance-for-sharepoint-vulnerability-cve-2025-53770
- NHS Digital cyber alert (vuln/patching urgency): https://digital.nhs.uk/cyber-alerts/2026/cc-4742
- AI accelerating attack speed (CrowdStrike report coverage): https://www.itpro.com/security/crowdstrike-says-ai-is-officially-supercharging-cyber-attacks-average-breakout-times-hit-just-29-minutes-in-2025-65-percent-faster-than-in-2024-and-some-attacks-take-just-seconds
We have created Professional High Quality Downloadable PDF’s at great prices specifically for Small and Medium UK Businesses our main website. Which include various helpful Cyber related documents and real world scenarios your business might experience, showing what to do and how to protect your business. Find them here.