Cyber attacks targeting businesses, government agencies and individuals rarely come from a single laptop. Modern cybercrime depends on a hidden layer of infrastructure that allows attackers to operate anonymously and keep their operations online.
One of the most important pieces of that infrastructure is bulletproof hosting.
Security researchers and law-enforcement agencies increasingly describe bulletproof hosting as a core component of the global cybercrime ecosystem. According to international cybercrime investigators, these hosting services provide a digital “safe haven” where criminals can run attacks while ignoring abuse complaints and takedown requests.
Understanding how bulletproof hosting works helps explain why attacks against UK and English-based networks can be difficult to shut down quickly.
What Is Bulletproof Hosting?

Abuse-Resistant Hosting Infrastructure
Bulletproof hosting (often abbreviated as BPH) refers to internet hosting services that deliberately ignore or resist abuse complaints about the content or activity hosted on their servers.
In simple terms, these providers rent servers to customers even when those customers are running illegal or harmful online operations.
Unlike legitimate hosting companies, which typically suspend accounts linked to malware or fraud, bulletproof hosts often promise customers they will ignore complaints, copyright notices and even some law-enforcement requests.
Typical activities hosted on these networks include:
- phishing websites
- malware download servers
- ransomware control panels
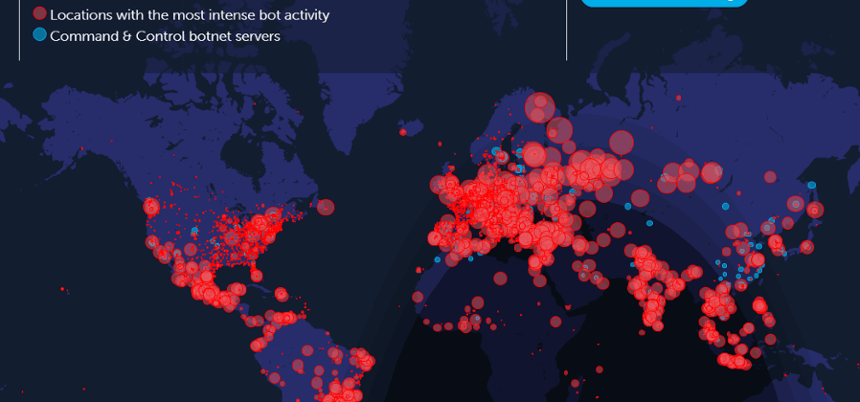
- botnet command-and-control infrastructure
- spam networks
- stolen data marketplaces
These services are often marketed directly in underground cybercrime forums.
Why Bulletproof Hosting Is Critical to Cybercrime
The Backbone of the Cybercrime Economy
Cybercrime is no longer a small-scale activity carried out by isolated hackers. It has evolved into a service-based economy where specialised providers supply tools and infrastructure.
Bulletproof hosting providers sit at the centre of this ecosystem.
International investigators say these services supply the technical environment criminals need to operate phishing networks, botnets and ransomware campaigns.
Because one hosting provider may support hundreds of criminal customers simultaneously, a single bulletproof hosting network can enable attacks across multiple countries.
Enabling Attacks on UK and English Networks
Cybercriminal groups targeting British organisations frequently rely on overseas infrastructure.
Attackers may:
- operate from one country
- rent servers from another
- register domains elsewhere
- route traffic through multiple global networks
This fragmented structure means the infrastructure behind attacks on English businesses, councils or schools may exist entirely outside UK jurisdiction.
Where Bulletproof Hosting Providers Operate

Jurisdictions With Weak Enforcement
Bulletproof hosting companies typically operate in jurisdictions where legal enforcement is weaker or slower.
Historically, researchers have identified BPH networks operating in regions such as:
- Eastern Europe
- parts of Asia
- offshore jurisdictions
- countries with limited cybercrime cooperation treaties
These locations make investigations slower and more complicated for Western law-enforcement agencies.
In many cases, hosting providers deliberately design their operations to exploit gaps in international law enforcement.
Famous Bulletproof Hosting Networks

Several major bulletproof hosting providers have been dismantled by international police operations.
Examples include:
- CyberBunker – A notorious host operating from a former NATO bunker, raided by German police in 2019.
- McColo – A US-based provider shut down in 2008 that was linked to global spam networks.
- LOLEKHosted – A hosting provider connected to ransomware infrastructure dismantled by authorities in 2023.
- CrazyRDP – A bulletproof hosting platform taken down in 2025 with around 250 servers seized during the investigation.
These cases demonstrate that although bulletproof hosting services attempt to resist takedowns, they remain vulnerable to coordinated international investigations.
Are Bulletproof Hosting Services Truly “Bulletproof”?

The Name Is Mostly Marketing
Security agencies emphasise that the term “bulletproof” is largely a marketing label used to attract cybercriminal customers.
In reality, these services are not immune to disruption or investigation.
Authorities can still target them by:
- seizing servers
- arresting administrators
- blocking domain names
- disrupting payment systems
- blacklisting IP address ranges
However, the process often requires cooperation between multiple countries.
Infrastructure Can Be Rebuilt Quickly
One reason bulletproof hosting appears resilient is that attackers can rebuild infrastructure rapidly.
Cybercriminals can rent new servers, register new domains and move operations to different providers within hours.
This means that even when authorities dismantle one network, the criminal group behind it may quickly establish another.
Expert Perspective
Security analysts frequently describe bulletproof hosting as a key enabler of cybercrime infrastructure.
Law-enforcement agencies note that these services provide criminals with a digital environment where attack infrastructure can remain online long enough to execute phishing campaigns, distribute malware and run ransomware negotiations.
Because these platforms support multiple criminal clients simultaneously, disrupting a single bulletproof host can sometimes dismantle hundreds of cybercriminal operations.
Why This Matters for UK Organisations
For British businesses and public organisations, the existence of bulletproof hosting means cyber attacks often originate from infrastructure designed to resist rapid shutdown.
This has several implications:
- malicious websites may remain online longer
- phishing campaigns can operate across multiple domains
- ransomware groups may maintain stable negotiation portals
- investigations require international cooperation
Understanding this infrastructure helps defenders recognise why cyber attacks sometimes persist even after victims report them.
Final Verdict
Bulletproof hosting is not a hacking technique but rather the infrastructure that allows cybercrime to operate at scale.
By offering abuse-resistant servers and ignoring takedown requests, these providers allow cybercriminals to run phishing campaigns, malware networks and ransomware operations for longer periods.
However, despite the intimidating name, these services are not invincible. International investigations, sanctions and server seizures continue to dismantle major bulletproof hosting networks around the world.
For organisations in the UK, recognising the role of bulletproof hosting provides valuable insight into the hidden infrastructure that powers many modern cyber attacks.
We have created Professional High Quality Downloadable PDF’s at great prices specifically for Small and Medium UK Businesses our main website. Which include various helpful Cyber related documents and real world scenarios your business might experience, showing what to do and how to protect your business. Find them here.





















