Today’s briefing covers the most relevant and high‑impact cyber security developments, starting with England, followed by the wider United Kingdom, with practical context on what these stories mean in the real world.
England
Major council IT disruption shows long recovery timelines after cyber attacks

Local authorities in England are still dealing with the after‑effects of significant cyber incidents, underlining how long recovery can take once systems are compromised.
Recent reporting highlights how councils affected by cyber attacks have had to rebuild systems from the ground up, often taking months to fully restore services. In some cases, authorities have had to revert to manual processes while networks were secured and rebuilt.
This reflects a wider pattern: cyber attacks against councils are no longer quick disruptions — they are extended operational crises.
Real‑world consequences
When a council’s systems go down, the impact spreads quickly:
- delays to housing and benefits processing
- disruption to planning and licensing services
- payment systems taken offline
- reduced communication with residents
Cyber security experts note that attackers often target councils because they provide essential services, meaning downtime creates immediate pressure.
Expert view
Public‑sector cyber specialists consistently warn that legacy IT systems and limited budgets leave some councils exposed. Even when systems are restored, recovery involves:
- resetting thousands of user accounts
- rebuilding servers and databases
- auditing systems for hidden threats
This explains why disruptions can last weeks or months rather than days.
Education sector facing sustained phishing and ransomware pressure

Cyber attacks targeting schools across England remain persistent, with phishing emails and ransomware continuing to be the most common threats.
Security assessments indicate that a large proportion of UK schools experience attempted breaches each year, with staff email accounts often the initial entry point.
Why schools are repeatedly targeted
Education environments combine several risk factors:
- high user numbers (students and staff)
- shared devices and networks
- limited dedicated cyber security staff
Recent incidents have shown that attackers can disrupt:
- email systems used by teachers
- online learning platforms
- safeguarding and administrative systems
Real‑world implications
When schools are hit by cyber incidents, the consequences go beyond IT:
- lessons disrupted or cancelled
- communication with parents affected
- sensitive student data potentially exposed
Experts increasingly stress that cyber security in education is now a safeguarding issue as well as a technical one.
United Kingdom
UK warned to stay alert as global cyber tensions rise

The UK’s cyber defence agency, the National Cyber Security Centre, continues to advise organisations to remain vigilant amid rising global cyber tensions.
Security experts warn that geopolitical conflicts are increasingly playing out in cyberspace, with attackers targeting organisations far beyond the immediate region of conflict.
What organisations should expect
Typical activity linked to geopolitical cyber campaigns includes:
- phishing emails designed to steal credentials
- scanning for vulnerable systems
- disruption attacks against websites and services
Even when the UK is not directly targeted, organisations may be affected because attackers often operate globally.
Expert insight
Cyber analysts emphasise that many of these attacks succeed due to basic security weaknesses, not advanced hacking techniques — making preventative measures critically important.
Growing concern over attacks targeting everyday devices and SMEs
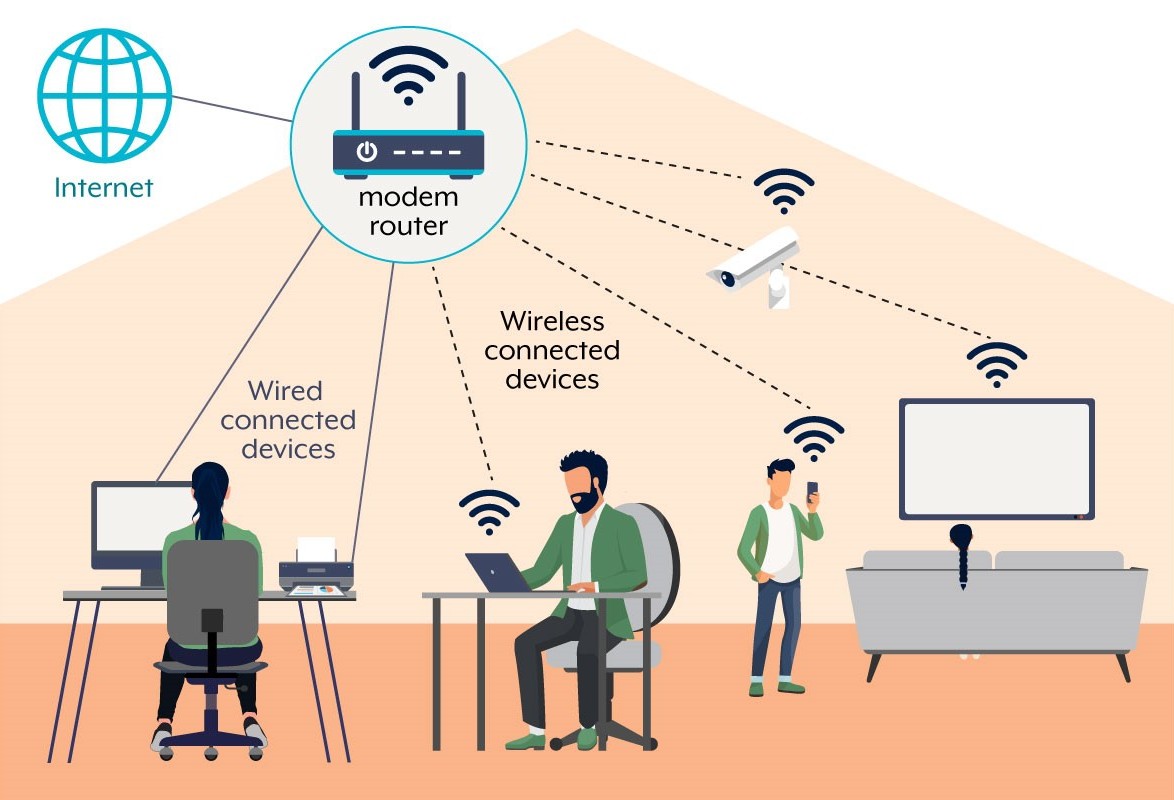
Security researchers are increasingly concerned about attacks targeting home routers and small business network devices, which are often overlooked.
Thousands of compromised devices globally are being used as part of botnets — networks of infected machines controlled by attackers.
Why this matters in the UK
Many UK households and small businesses:
- rarely update router firmware
- use default or weak passwords
- rely on ageing network equipment
This makes them easy targets for attackers looking to:
- hide malicious activity
- launch attacks on other organisations
- gain access to business networks
Real‑world impact
A compromised router may not show obvious signs of attack, but it can:
- slow down internet connections
- expose sensitive data
- provide a gateway into business systems
For small businesses in particular, this can become a serious but invisible security risk.
Government pushing ahead with stronger cyber resilience measures
The UK government continues to strengthen its cyber resilience strategy through improved monitoring and proposed legislation.
The planned Cyber Security and Resilience Bill is expected to expand requirements for organisations responsible for critical digital services.
What this means in practice
The proposed changes aim to:
- enforce stronger security standards
- improve incident reporting
- increase accountability for cyber resilience
Experts believe this reflects a broader shift: cyber security is now seen as essential national infrastructure protection, not just an IT concern.
Key Cyber Themes Today
- Cyber incidents in England are causing long‑lasting disruption to public services.
- Schools remain one of the most consistently targeted sectors.
- Global tensions are increasing cyber risks for UK organisations.
- Everyday devices such as routers are becoming key attack points.
- Government is strengthening national cyber resilience through policy and legislation.
Reality check:
Across the UK, the majority of cyber incidents still begin with simple, preventable weaknesses — weak passwords, outdated systems or a single phishing email. Strong fundamentals remain the most effective defence.
We have created Professional High Quality Downloadable PDF’s at great prices specifically for Small and Medium UK Businesses our main website. Which include various helpful Cyber related documents and real world scenarios your business might experience, showing what to do and how to protect your business. Find them here.