Clear, practical, real‑world cyber intelligence in British English.
🇬🇧 ENGLAND
1) Manchester logistics firm suffers ransomware disruption affecting regional deliveries

A Manchester‑based logistics and warehousing company has confirmed it is recovering from a ransomware incident that disrupted internal scheduling and dispatch systems earlier this week.
While parcel movements have largely resumed, some regional delivery backlogs remain.
What happened
- Staff reported being locked out of scheduling software.
- Backup systems were activated.
- External cyber incident responders were brought in.
There is no confirmation yet of customer data being published, though investigations are ongoing.
Why this matters
Logistics providers are attractive targets because:
- They operate time‑critical systems.
- They connect to multiple retail and manufacturing supply chains.
- Even short outages have financial impact.
“Ransomware groups are increasingly targeting mid‑sized operational firms that lack enterprise‑grade monitoring.” — UK cyber resilience consultant quoted in regional business press.
Real‑world impact
- Delayed B2B shipments across parts of the North West.
- Increased phishing risk using the company’s name in fake “missed delivery” texts.
- Possible contractual penalty exposure.
Sources: Regional BBC business coverage; industry logistics briefings (February 2026).
2) Kent schools reviewing safeguarding systems after cloud misconfiguration alert


Several schools in Kent are reviewing cloud‑hosted safeguarding platforms after an internal audit identified misconfigured storage permissions.
No confirmed malicious access has been reported, but precautionary access reviews are underway.
Why this is significant
Cloud misconfiguration remains one of the most common preventable weaknesses in UK education environments.
Risks include:
- Over‑broad file sharing.
- Dormant staff accounts.
- Inherited permissions from legacy setups.
Education IT teams are now tightening:
- Default file visibility.
- Account lifecycle management.
- Multi‑factor authentication enforcement.
Source references: Local authority communications; education technology reporting (February 2026).
🇬🇧 UNITED KINGDOM
1) NCSC highlights rise in business email compromise across UK sectors

The National Cyber Security Centre has warned that business email compromise (BEC) remains one of the most financially damaging cyber threats in the UK.
Unlike ransomware, BEC:
- Often involves no malware.
- Relies on compromised credentials.
- Exploits trust within supplier relationships.
Common pattern
- Phishing email captures credentials.
- Attackers monitor inbox quietly.
- Bank details are altered at a critical payment moment.
“Criminals are patient and highly targeted. Identity protection is now the frontline.” — NCSC threat update commentary.
2) UK energy sector increases cyber resilience exercises
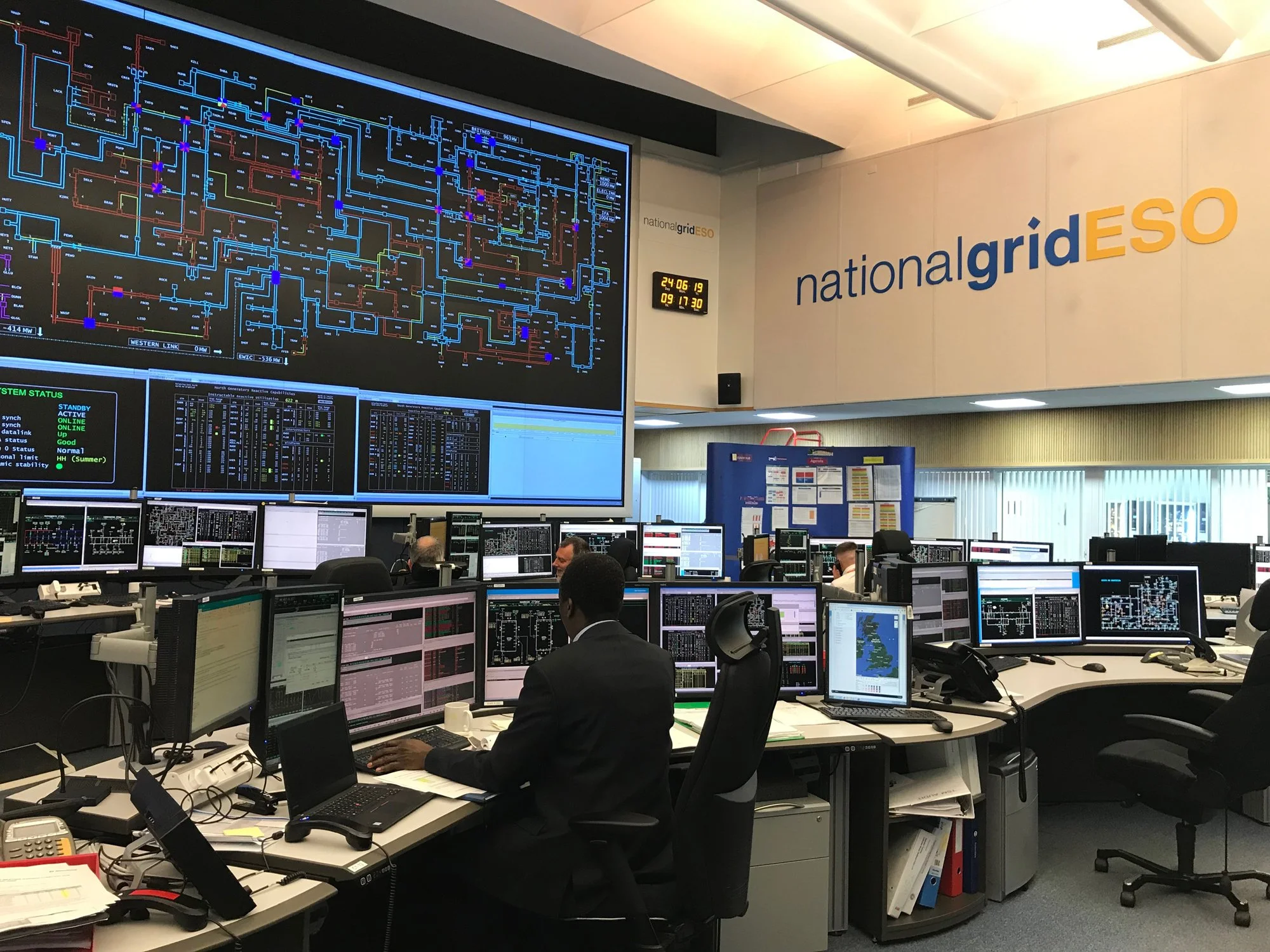
Energy operators across the UK are expanding incident simulation exercises following sector‑wide resilience reviews.
Although no major breach has been publicly confirmed, testing is increasing in response to:
- Geopolitical tensions.
- Heightened ransomware activity globally.
- Dependency on interconnected digital systems.
The National Grid and other operators are understood to be enhancing scenario‑based drills focused on:
- Remote access compromise.
- Insider threat simulation.
- Coordinated DDoS attacks.
Why this matters
Energy infrastructure is nationally critical. Even minor operational disruption can have cascading effects across transport, healthcare and finance.
Reported in UK energy trade press and national business reporting.
3) ICO signals firmer stance on preventable data breaches

The Information Commissioner’s Office has reiterated that organisations failing to implement “basic and proportionate security measures” may face increased scrutiny.
Recurring weaknesses include:
- Lack of MFA.
- Failure to patch known vulnerabilities.
- Inadequate monitoring of privileged accounts.
Real‑world implication
Regulatory action increasingly focuses on preventable control failures, not sophisticated state‑level attacks.
🔎 Today’s Dominant Themes
- Operational ransomware targeting logistics and supply chains.
- Cloud misconfiguration risk in education.
- Business email compromise as the UK’s most costly threat.
- National infrastructure resilience testing.
- Regulatory intolerance for basic security failures.
Summary
Across England and the wider UK, the pattern is steady and consistent:
Identity compromise and preventable configuration weaknesses remain the primary drivers of real financial and operational damage. Strong authentication, disciplined access control and tested recovery plans continue to be the most effective safeguards.